
Microsoft is addressing 118 vulnerabilities this October 2024 Patch Tuesday. Microsoft has evidence of in-the-wild exploitation and/or public disclosure for five of the vulnerabilities published today, although it does not rate any of these as critical (yet). Of those five, Microsoft lists two as exploited in the wild, and both of these are now listed on CISA KEV. Microsoft is also patching three further critical remote code execution (RCE) vulnerabilities today. Three browser vulnerabilities have already been published separately this month, and are not included in the total.
Somewhat unusually, we’ll take a look at two of the three critical RCEs published today — CVE-2024-43468 and CVE-2024-43582 — before moving on to the arguably somewhat-less- threatening zero-day vulnerabilities patched today.
Microsoft Configuration Manager: pre-auth RCE
Microsoft Configuration Manager receives a patch for the only vulnerability published by Microsoft today with a CVSS base score of 9.8. Although Microsoft doesn’t tag it as either publicly disclosed or exploited-in-the-wild, the advisory for CVE-2024-43468 appears to describe a no-interaction, low complexity, unauthenticated network RCE against Microsoft Configuration Manager. Exploitation is achieved by sending specially-crafted malicious requests, and leads to code execution in the context of the Configuration Manager server or its underlying database. The relevant update is installed within the Configuration Manager console, and requires specific administrator actions that Microsoft describes in detail in a generic series of articles. Further information and several specific required steps are described in KB29166583.
Confusingly, this KB29166583 was first published over a month ago on 2024-09-04, and was then subsequently unpublished and republished on 2024-09-18, all without any mention of CVE-2024-43468, which was published only today and which KB29166583 apparently remediates. Defenders should read the available documentation carefully, and then probably read it again for good measure.
RPD RPC: pre-auth RCE
Any RDP Server critical RCE is worth patching quickly. CVE-2024-43582 is a pre-auth critical RCE in the Remote Desktop Protocol Server. Exploitation requires an attacker to send deliberately-malformed packets to a Windows RPC host, and leads to code execution in the context of the RPC service, although what this means in practice may depend on factors including RPC Interface Restriction configuration on the target asset. One silver lining: attack complexity is high, since the attacker must win a race condition to access memory improperly.
Winlogon: zero-day EoP
Who doesn’t love a good elevation of privilege vulnerability? Weary blue teamers who see the words “publicly disclosed” on a brand-new advisory know the answer. CVE-2024-43583 describes a flaw in Winlogon which gets an attacker all the way to SYSTEM via abuse of a third-party Input Method Editor (IME) during the sign-on process. The supplementary KB5046254 article explains that the 2024-10-08 patches disable non-Microsoft IME during the sign-in process. On that basis, outright removal of third-party IME is a mitigation available to anyone who is not able to apply today’s patches immediately.
Attack surface reduction is always worth considering, and removal of third-party IMEs certainly accomplishes that. Anyone who needs to keep a third-party IME can still do so, but once today’s patches are applied, that third-party IME will be disabled — only in the context of the sign-in process — to prevent exploitation of CVE-2024-43583. Although Microsoft doesn’t quite spell it out, the only reasonable interpretation of the available information is that an asset with no first-party/Microsoft IME installed would remain vulnerable after patching, since otherwise no IME would be available when attempting to sign in. Use of third-party IME is more likely to be a concern in mixed-language or non-English-speaking contexts. The disclosure process around this vulnerability may not have been entirely smooth; back in September, one of the researchers credited with the discovery expressed discontent with MSRC via X-formerly-known-as-Twitter.
Hyper-V: zero-day container escape
CVE-2024-20659 describes a publicly-disclosed security feature bypass in Hyper-V. Microsoft describes exploitation as both less likely and highly complex. An attacker must be both lucky and resourceful, since only UEFI-enabled hypervisors with certain unspecified hardware are vulnerable, and exploitation requires coordination of a number of factors followed by a well-timed reboot. All this after first achieving a foothold on the same network — although in this context, this likely means access to a VM on the target hypervisor, rather than some other location on the same subnet. The prize for successful exploitation is compromise of the hypervisor kernel.
MSHTML: zero-day XSS
CVE-2024-43573 is an exploited-in-the-wild spoofing vulnerability in MSHTML for which Microsoft is also aware of functional public exploit code; the advisory lists CWE-79 as the weakness, which translates to cross-site scripting (XSS). The advisory is sparse on further detail, although Windows Server 2012/2012 R2 admins who typically install Security Only updates should note that Microsoft is encouraging installation of the Monthly Rollups to ensure remediation in this case. The low CVSSv3 base score of 6.5 reflects the requirement for user interaction and the lack of impact to integrity or availability; a reasonable assumption might be that exploitation leads to improper disclosure of sensitive data, but no other direct effect on the target asset.
cURL: zero-day RCE
Microsoft is most famous for its closed source products, but has cautiously softened its stance on open source considerably in the past quarter century or so. Windows has included components of cURL for almost seven years at this point, along with various other open source components; Microsoft does patch these from time to time, although not always as quickly as defenders might like. Today’s patches for CVE-2024-6197, a publicly-disclosed RCE vulnerability in cURL, continue that trend.
The Microsoft advisory for CVE-2024-6197 clarifies that Windows does not ship libcurl, only the curl command line, but that’s still vulnerable and thus in scope for a fix. Exploitation requires that the user connect to a malicious server controlled by the attacker, and code execution is presumably in the context of the user launching the curl CLI tool on the Windows asset. The cURL project advisory for CVE-2024-6197 was originally published on 2024-07-24, and offers further detail from their perspective. Interestingly, the cURL project describes the most likely outcome of exploitation as a crash, and does not specifically mention RCE, although it is careful not to exclude the possibility of unspecified “more serious results,” which could well mean RCE. Microsoft rates this vulnerability as important, which is on track with the CVSS base score of 8.8.
Management Console: zero-day RCE
CVE-2024-43572 rounds out today’s five zero-day vulnerabilities, and describes a low-complexity, no-user-interaction RCE in Microsoft Management Console. Microsoft is aware of both public functional exploit code and in-the-wild exploitation. The vulnerability is exploited when a user downloads and opens a specially-crafted malicious Microsoft Saved Console (MSC) file, so there’s no suggestion here that the Management Console is vulnerable via network attack. Today’s patches prevent untrusted MSC files from being opened, although the advisory does not describe how Windows will know what’s trusted and what isn’t. Microsoft has chosen to map CVE-2024-43572 to CWE-70, which is a very broad category, the use of which is explicitly discouraged by MITRE.
VS Code Arduino extension: cloud critical RCE
A third critical RCE patched today is hopefully less concerning than its siblings. CVE-2024-43488 is in the Visual Studio Code extension for Arduino, and Microsoft notes that the vulnerability documented by this CVE requires no customer action to resolve. A reasonable question is: what does “no action required” really mean here? Within the advisory, Microsoft both claims to have fully mitigated the vulnerability, and also that there is no plan to fix the vulnerability. As confusing as that all sounds, perhaps the most important takeaway here is that Microsoft is now issuing cloud service CVEs in a stated effort to improve transparency. It’s not clear when the vulnerability was first introduced or when it was remediated, but nevertheless the recent expansion into a whole new class of CVEs is a welcome step by Microsoft.
SharePoint: EoP to SYSTEM
A sparse advisory for CVE-2024-43503, which is an elevation of privilege vulnerability which leads to SYSTEM. Advisories for similar vulnerabilities typically describe the specific SharePoint privileges required, but this one does not, so a reasonable assumption might be that the requirement here is simply minimal Site Member privileges.
Microsoft lifecycle update
Today sees the end of support for Windows 11 22H2 for Home, Pro, Pro Education, Pro for Workstations, and SE editions, as well as for Windows 11 21H2 for Education, Enterprise, and Enterprise multi-session editions. Server 2012 and Server 2012 R2 pass into Year 2 of ESU. Windows Embedded POSReady — the POS stands for Point-of-Sale — receives its final ESU updates today, and that might just be the last gasp for Windows 7 as a whole. As well as patching today’s critical RCE CVE-2024-43468, Intune admins still using Configuration Manager 2303 should look to upgrade to a newer version immediately, because support ends (somewhat unusually) on Thursday this week.
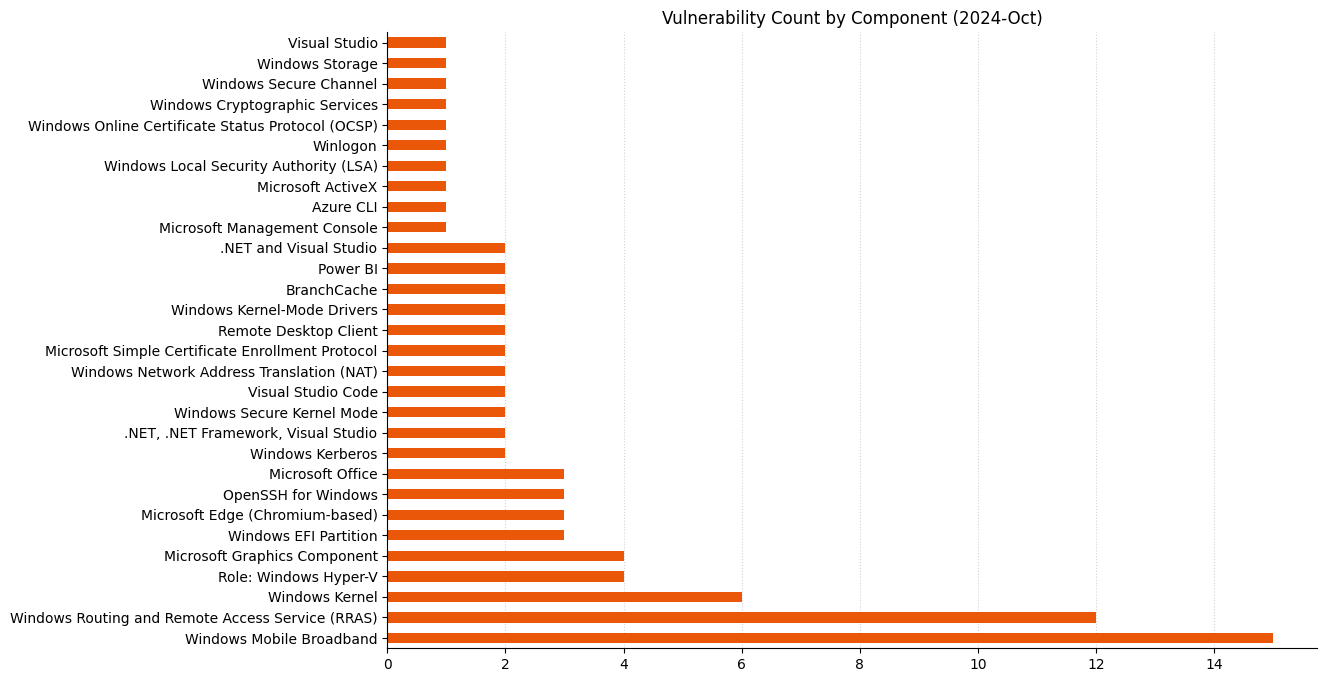
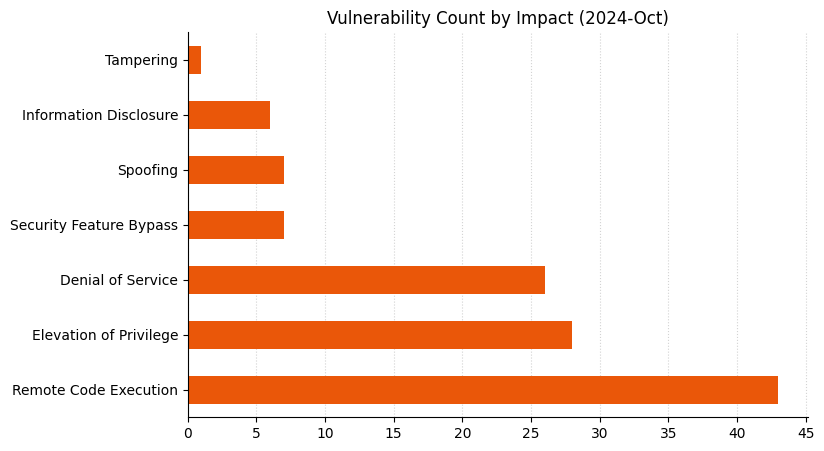
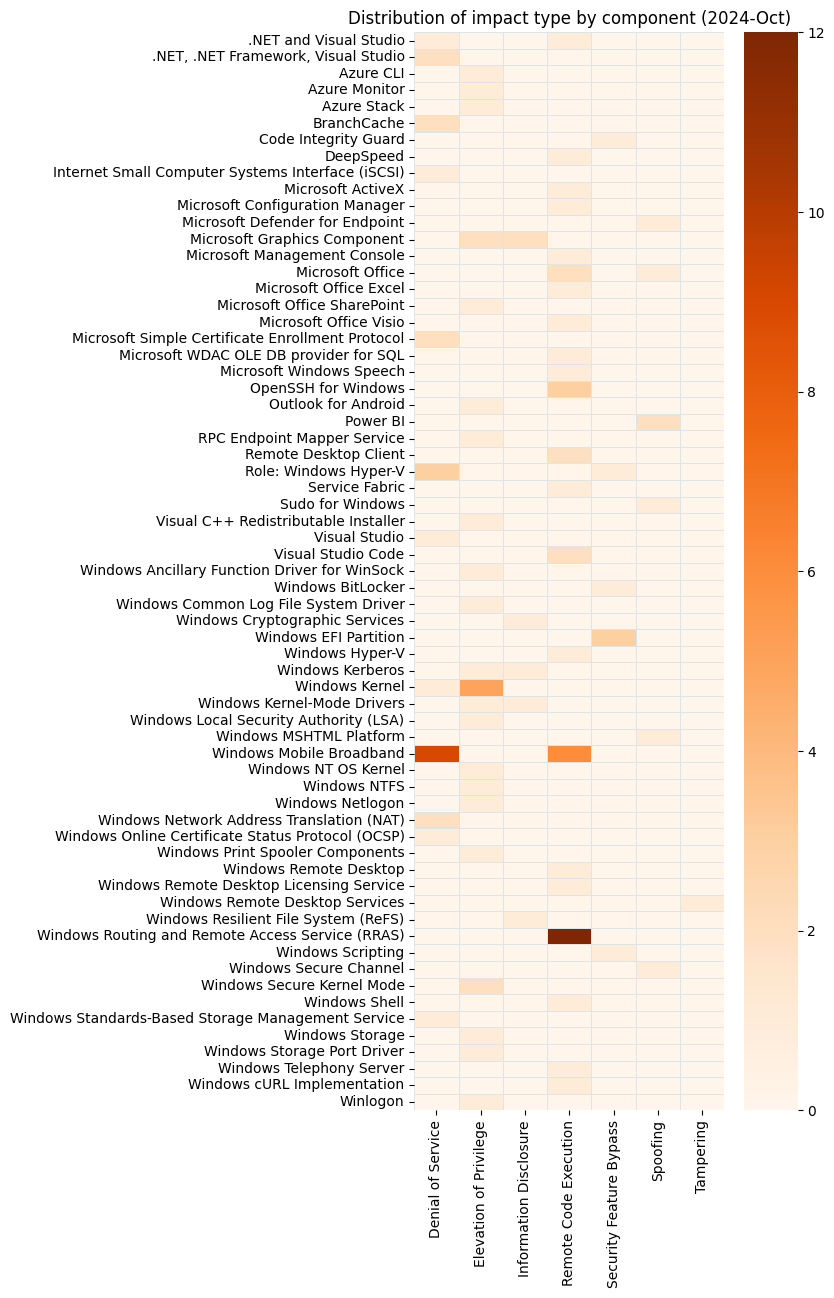
Summary charts
Summary tables
Apps vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-43604 | Outlook for Android Elevation of Privilege Vulnerability | No | No | 5.7 |
Azure vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38179 | Azure Stack Hyperconverged Infrastructure (HCI) Elevation of Privilege Vulnerability | No | No | 8.8 |
| CVE-2024-43591 | Azure Command Line Integration (CLI) Elevation of Privilege Vulnerability | No | No | 8.7 |
| CVE-2024-38097 | Azure Monitor Agent Elevation of Privilege Vulnerability | No | No | 7.1 |
| CVE-2024-43480 | Azure Service Fabric for Linux Remote Code Execution Vulnerability | No | No | 6.6 |
Browser vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-9370 | Chromium: CVE-2024-9370 Inappropriate implementation in V8 | No | No | N/A |
| CVE-2024-9369 | Chromium: CVE-2024-9369 Insufficient data validation in Mojo | No | No | N/A |
| CVE-2024-7025 | Chromium: CVE-2024-7025 Integer overflow in Layout | No | No | N/A |
Developer Tools vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-43488 | Visual Studio Code extension for Arduino Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43497 | DeepSpeed Remote Code Execution Vulnerability | No | No | 8.4 |
| CVE-2024-38229 | .NET and Visual Studio Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-43590 | Visual C++ Redistributable Installer Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43483 | .NET, .NET Framework, and Visual Studio Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-43484 | .NET, .NET Framework, and Visual Studio Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-43485 | .NET and Visual Studio Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-43601 | Visual Studio Code for Linux Remote Code Execution Vulnerability | No | No | 7.1 |
| CVE-2024-43603 | Visual Studio Collector Service Denial of Service Vulnerability | No | No | 5.5 |
ESU Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38124 | Windows Netlogon Elevation of Privilege Vulnerability | No | No | 9 |
| CVE-2024-43518 | Windows Telephony Server Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43608 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43607 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-38265 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43453 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-38212 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43549 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43564 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43589 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43592 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43593 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43611 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43532 | Remote Registry Service Elevation of Privilege Vulnerability | No | No | 8.8 |
| CVE-2024-43599 | Remote Desktop Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43519 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43517 | Microsoft ActiveX Data Objects Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43583 | Winlogon Elevation of Privilege Vulnerability | No | Yes | 7.8 |
| CVE-2024-38261 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-43514 | Windows Resilient File System (ReFS) Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43509 | Windows Graphics Component Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43556 | Windows Graphics Component Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43501 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43563 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43560 | Microsoft Windows Storage Port Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43572 | Microsoft Management Console Remote Code Execution Vulnerability | Yes | Yes | 7.8 |
| CVE-2024-38262 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability | No | No | 7.5 |
| CVE-2024-43545 | Windows Online Certificate Status Protocol (OCSP) Server Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-43521 | Windows Hyper-V Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-43567 | Windows Hyper-V Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-43541 | Microsoft Simple Certificate Enrollment Protocol Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-43544 | Microsoft Simple Certificate Enrollment Protocol Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-43515 | Internet Small Computer Systems Interface (iSCSI) Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-43506 | BranchCache Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-38149 | BranchCache Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-43550 | Windows Secure Channel Spoofing Vulnerability | No | No | 7.4 |
| CVE-2024-43553 | NT OS Kernel Elevation of Privilege Vulnerability | No | No | 7.4 |
| CVE-2024-43535 | Windows Kernel-Mode Driver Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-37976 | Windows Resume Extensible Firmware Interface Security Feature Bypass Vulnerability | No | No | 6.7 |
| CVE-2024-37982 | Windows Resume Extensible Firmware Interface Security Feature Bypass Vulnerability | No | No | 6.7 |
| CVE-2024-37983 | Windows Resume Extensible Firmware Interface Security Feature Bypass Vulnerability | No | No | 6.7 |
| CVE-2024-37979 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 6.7 |
| CVE-2024-43512 | Windows Standards-Based Storage Management Service Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-43573 | Windows MSHTML Platform Spoofing Vulnerability | Yes | Yes | 6.5 |
| CVE-2024-43547 | Windows Kerberos Information Disclosure Vulnerability | No | No | 6.5 |
| CVE-2024-43534 | Windows Graphics Component Information Disclosure Vulnerability | No | No | 6.5 |
| CVE-2024-43570 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 6.4 |
| CVE-2024-43513 | BitLocker Security Feature Bypass Vulnerability | No | No | 6.4 |
| CVE-2024-43520 | Windows Kernel Denial of Service Vulnerability | No | No | 5 |
| CVE-2024-43456 | Windows Remote Desktop Services Tampering Vulnerability | No | No | 4.8 |
Mariner Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-6197 | Open Source Curl Remote Code Execution Vulnerability | No | Yes | 8.8 |
Microsoft Office vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-43503 | Microsoft SharePoint Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43505 | Microsoft Office Visio Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-43576 | Microsoft Office Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-43616 | Microsoft Office Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-43504 | Microsoft Excel Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-43609 | Microsoft Office Spoofing Vulnerability | No | No | 6.5 |
SQL Server vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-43612 | Power BI Report Server Spoofing Vulnerability | No | No | 6.9 |
| CVE-2024-43481 | Power BI Report Server Spoofing Vulnerability | No | No | 6.5 |
System Center vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-43468 | Microsoft Configuration Manager Remote Code Execution Vulnerability | No | No | 9.8 |
| CVE-2024-43614 | Microsoft Defender for Endpoint for Linux Spoofing Vulnerability | No | No | 5.5 |
Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-43533 | Remote Desktop Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43574 | Microsoft Speech Application Programming Interface (SAPI) Remote Code Execution Vulnerability | No | No | 8.3 |
| CVE-2024-43582 | Remote Desktop Protocol Server Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-30092 | Windows Hyper-V Remote Code Execution Vulnerability | No | No | 8 |
| CVE-2024-43551 | Windows Storage Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43516 | Windows Secure Kernel Mode Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43528 | Windows Secure Kernel Mode Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43527 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43584 | Windows Scripting Engine Security Feature Bypass Vulnerability | No | No | 7.7 |
| CVE-2024-43562 | Windows Network Address Translation (NAT) Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-43565 | Windows Network Address Translation (NAT) Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-38129 | Windows Kerberos Elevation of Privilege Vulnerability | No | No | 7.5 |
| CVE-2024-43575 | Windows Hyper-V Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-38029 | Microsoft OpenSSH for Windows Remote Code Execution Vulnerability | No | No | 7.5 |
| CVE-2024-43552 | Windows Shell Remote Code Execution Vulnerability | No | No | 7.3 |
| CVE-2024-43529 | Windows Print Spooler Elevation of Privilege Vulnerability | No | No | 7.3 |
| CVE-2024-43502 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.1 |
| CVE-2024-20659 | Windows Hyper-V Security Feature Bypass Vulnerability | No | Yes | 7.1 |
| CVE-2024-43581 | Microsoft OpenSSH for Windows Remote Code Execution Vulnerability | No | No | 7.1 |
| CVE-2024-43615 | Microsoft OpenSSH for Windows Remote Code Execution Vulnerability | No | No | 7.1 |
| CVE-2024-43522 | Windows Local Security Authority (LSA) Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-43511 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-43525 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | No | No | 6.8 |
| CVE-2024-43526 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | No | No | 6.8 |
| CVE-2024-43543 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | No | No | 6.8 |
| CVE-2024-43523 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | No | No | 6.8 |
| CVE-2024-43524 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | No | No | 6.8 |
| CVE-2024-43536 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | No | No | 6.8 |
| CVE-2024-43537 | Windows Mobile Broadband Driver Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-43538 | Windows Mobile Broadband Driver Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-43540 | Windows Mobile Broadband Driver Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-43542 | Windows Mobile Broadband Driver Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-43555 | Windows Mobile Broadband Driver Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-43557 | Windows Mobile Broadband Driver Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-43558 | Windows Mobile Broadband Driver Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-43559 | Windows Mobile Broadband Driver Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-43561 | Windows Mobile Broadband Driver Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-43546 | Windows Cryptographic Information Disclosure Vulnerability | No | No | 5.6 |
| CVE-2024-43571 | Sudo for Windows Spoofing Vulnerability | No | No | 5.6 |
| CVE-2024-43500 | Windows Resilient File System (ReFS) Information Disclosure Vulnerability | No | No | 5.5 |
| CVE-2024-43554 | Windows Kernel-Mode Driver Information Disclosure Vulnerability | No | No | 5.5 |
| CVE-2024-43508 | Windows Graphics Component Information Disclosure Vulnerability | No | No | 5.5 |
| CVE-2024-43585 | Code Integrity Guard Security Feature Bypass Vulnerability | No | No | 5.5 |
Source: Rapid7
Source Link: https://blog.rapid7.com/2024/10/08/patch-tuesday-october-2024/