Co-authored by Yaniv Allender and Anna Sirokova

Introduction
Ransomware remains a major threat, causing significant disruption and financial losses to organizations across various sectors. Cybercriminal groups behind these attacks constantly adapt their methods to maximize damage and profit.
At Rapid7, we actively monitor new cyber threats, keeping an eye on ransomware groups and their changing tactics. In early 2025, we came across a channel promoting itself as Babuk Locker. Since the original group had shut down in 2021, we decided to investigate whether this was a rebrand or a new threat. Several underground forums and Telegram channels started mentioning ‘Babuk Locker 2.0,’ with some actors taking credit for recent attacks. Since Babuk’s leaked source code in 2021 had led to many spin-off ransomware strains, we wanted to find out whether this was a real comeback or just another group using Babuk’s name.
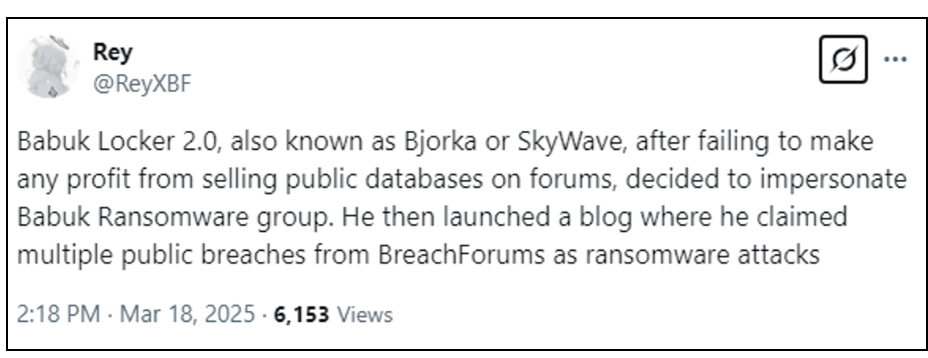
We started by gathering intelligence from dark web marketplaces, hacker forums, and private Telegram groups. We saw a rise in discussions about Babuk’s return, often linked to two groups, ‘Skywave’ and ‘Bjorka.’ These actors claimed responsibility for major attacks, and their leak sites suggested they might be working with other cybercriminal groups.
This blog delves into the potential revival of Babuk Locker 2.0, its alleged operators, and their activities. We analyze the involvement of ‘Skywave’ and ‘Bjorka,’ their claimed victims, and the evolution of Babuk’s Ransomware-as-a-Service (RaaS) model. Our findings include technical analysis, victimology, and the broader risks posed by this campaign.
Operators: Skywave and Bjorka
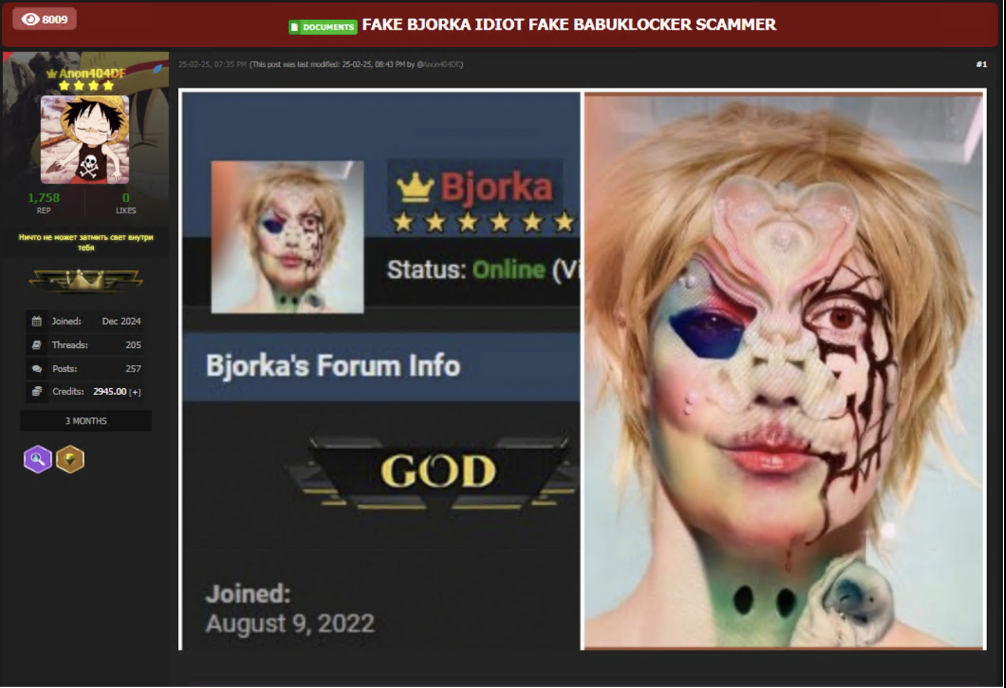
While monitoring Babuk Locker 2.0 activity, we identified two key groups linked to its operations—Skywave and Bjorka. These groups frequently appeared in discussions on underground forums and Telegram channels, claiming responsibility for attacks and promoting Babuk-related leaks. Our analysis suggests that these groups play a significant role in Babuk Locker 2.0’s activities, either as affiliates or key operators.
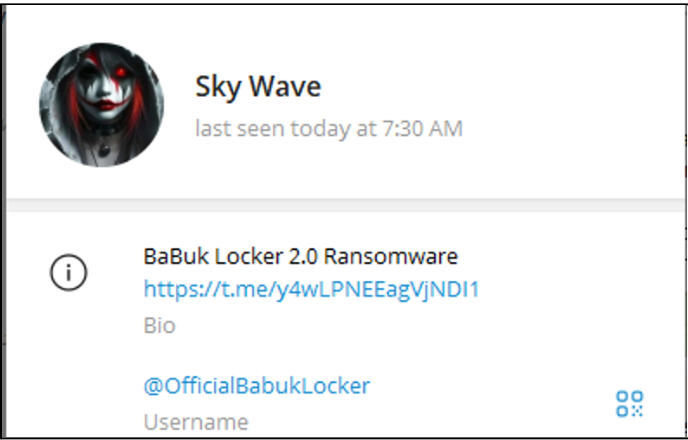
Skywave
Skywave is a recently identified threat actor known for allegedly executing cyberattacks against various high-profile organizations and government agencies. Their operations have raised concerns within the cybersecurity community due to the sensitivity and volume of the data reportedly compromised, as well as the anonymity of the operator. Skywave is suspected of operating multiple Telegram channels under different aliases, some of which have been flagged as scams and removed by Telegram.
The specific TTPs employed by Skywave remain undisclosed, leaving room for speculation regarding their infiltration and data exfiltration methods. Since late 2024, Skywave has maintained its presence on various platforms, such as Telegram, DarkForums, and the dedicated Babuk Locker 2.0 DLS, where they have been sharing leaked data from their allegedly recent attacks. Victim lists indicate a focus on high-profile organizations with sensitive data.
Bjorka
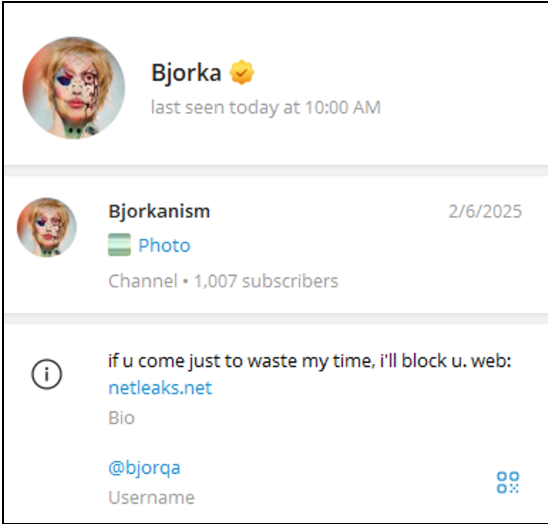
Bjorka is a threat actor mainly known for allegedly breaching Indonesian government and citizen data, often leaking sensitive information as a form of hacktivism. The alias gained prominence in 2022 with a series of high-profile data leaks, first making headlines in March by exposing over 105 million Indonesian voter records. Throughout 2022, Bjorka targeted multiple institutions, leaking personal data to highlight security flaws and criticize policies. By August 2022, Bjorka joined BreachForums, where they are sharing large databases from breached telecom services. Authorities attempted to identify the hacker, even arresting an individual, but Bjorka mocked the effort, claiming the wrong person was caught. The threat actor is active on BreachForums and Telegram and owns a personal leak site (netleaks[.]net) to distribute stolen data and engage followers.
Babuk Locker 2.0/Babuk-Bjorka
Since February 2025, Skywave has claimed ownership on at least 5 different Telegram channels and posts daily about their previous and current victims. Throughout the research, we found dozens of newly created Telegram channels with the names ‘Babuk Locker 2.0’, ‘Babuk 2.0 Ransomware Affiliates’, etc. Some of which overlapped with one another. Additionally, several channels were labeled as scams by Telegram itself and were unavailable a couple of days after they were created.

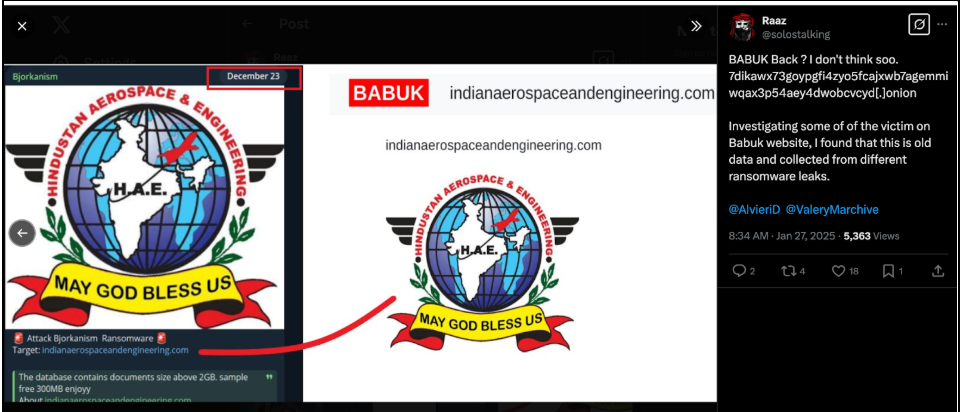
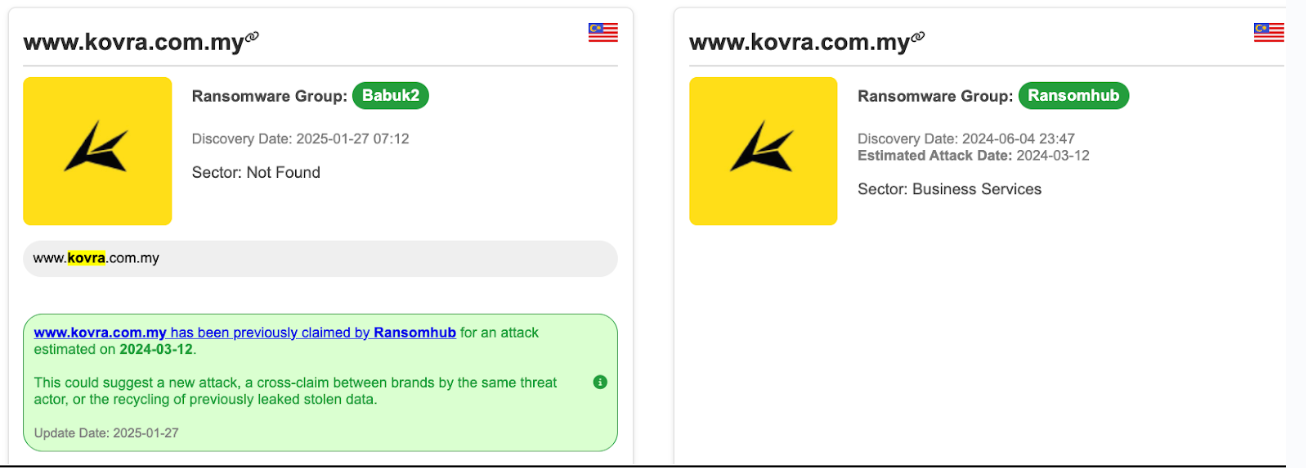
During our research, we noticed the consistent amplification of the Babuk 2.0 content by Bjorka on their Telegram channel. Speculation about the possible affiliation between Babuk and Bjorka rose due to the overlap of victims, such as the case of ‘Hindustan Aerospace & Engineering’ from India. The organization was initially reported as a victim of Bjorka in December 2023, and again as a victim of Babuk as of March 2025.
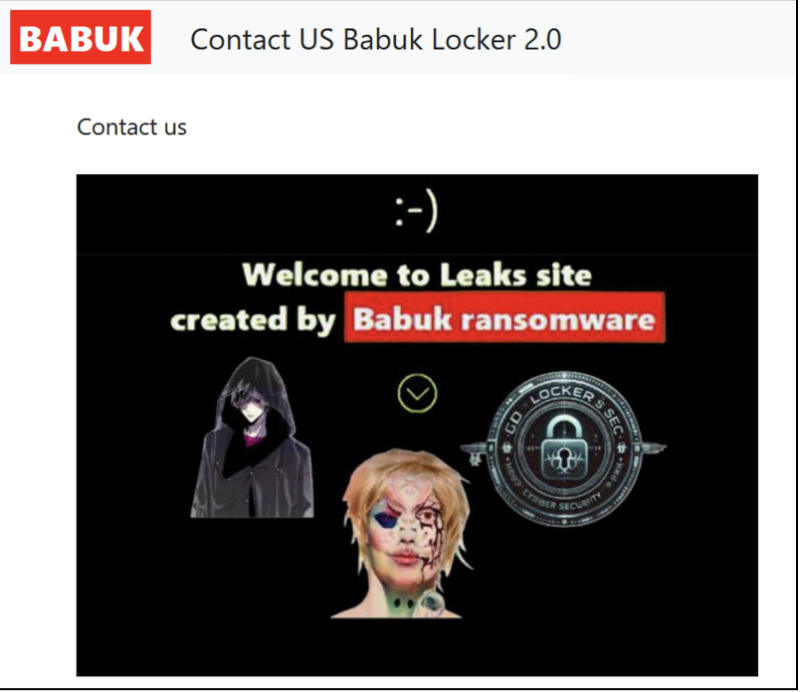
Further evidence of a possible collaboration between the threat actors emerges from the ‘Contact Us’ tab on Babuk’s DLS, where the logos of Skywave and Bjorka appear next to each other, as well as another possible affiliate named GD Locker Sec.
Technical Analysis
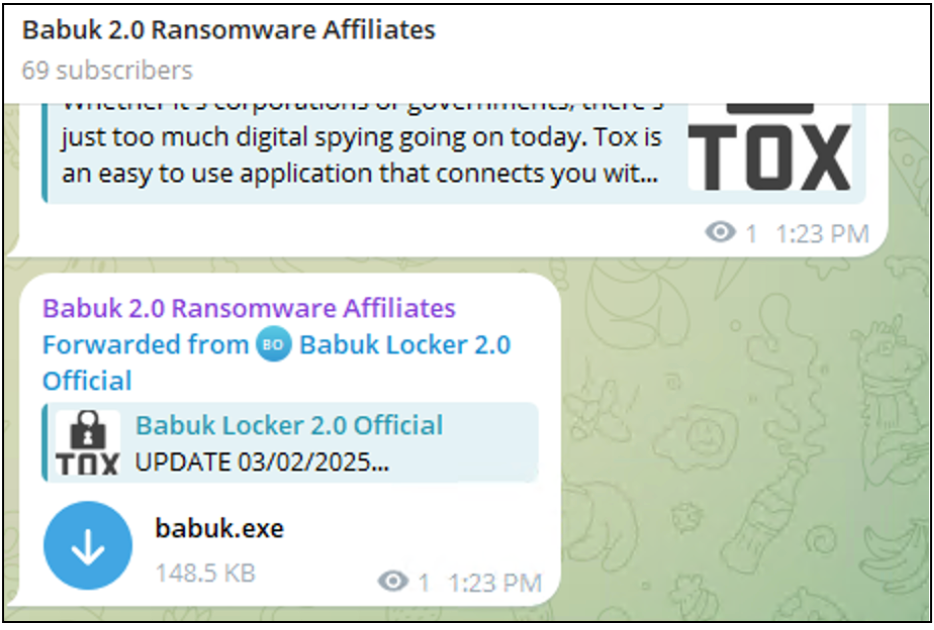
A sample named babuk.exe SHA-256 3facc153ed82a72695ee2718084db91f85e2560407899e1c7f6938fd4ea011e9 was initially shared on the Telegram channel “Babuk 2.0 Ransomware Affiliates”, before being forwarded to another operational account. Upon analysis, it turned out not to be Babuk Locker at all, but rather LockBit 3.0 also known as LockBit Black. This case is yet another example of the well-established trend: threat actors rebranding ransomware strains, whether to confuse researchers, lure affiliates, or just keep the marketing fresh. Either way, babuk.exe is just LockBit 3.0/Black wearing a fake name.
LockBit 3.0 Overview
LockBit 3.0/Black, is a ransomware variant that shares similarities with BlackMatter ransomware. On September 21, 2022, a user named @ali_qushji leaked the LockBit 3.0 builder on Twitter. The leak code made it easy for the least skilled attackers to join the game.
Encryption Methods
An analyzed sample of LockBit 3.0 uses a combination of AES-256 and RSA-2048 encryption. AES-256 is used to encrypt victim files and RSA-2048 encryption used to encrypt the AES key, ensuring decryption is impossible without the attacker’s private key.
Terminated Processes and services
LockBit 3.0 terminates various applications and system processes (the full list is in the table below) most likely to maximize encryption efficiency and prevent file access conflicts. It also disables key security and backup services to limit recovery possibilities and increase impact.
| Terminated Processes | Terminated Services |
|---|---|
| sql | vss |
| oracle | sql |
| ocssd | svc |
| dbsnmp | memtas |
| synctime | mepocs |
| agntsvc | msexchange |
| isqlplussvc | sophos |
| xfssvccon | veeam |
| mydesktopservice | backup |
| ocautoupds | GxVss |
| encsvc | GxBlr |
| firefox | GxFWD |
| tbirdconfig | GxCVD |
| mydesktopqos | GxCIMgr |
| ocomm | |
| dbeng50 | |
| sqbcoreservice | |
| excel | |
| infopath | |
| msaccess | |
| mspu | |
| onenote | |
| outlook | |
| powerpnt | |
| steam | |
| thebat | |
| thunderbird | |
| visio | |
| winword | |
| wordpad | |
| notepad | |
| calc | |
| wuauclt | |
| onedrive |
Active Directory Enumeration
LockBit 3.0 uses logoncli_DsGetDcNameW API function used for Active Directory (AD) enumeration. To brute-force AD accounts, analyzed LockBit 3.0 sample came preloaded with Base64-encoded username and password combinations decoded and listed below.
| Username | Password |
|---|---|
| bad.lab | Qwerty |
| Administrator | 123QWEqwe |
| @#Admin2 | P@ssw0rd |
| Administrator | P@ssw0rd |
| Administrator | Qwerty |
| Administrator | 123QWEqwe |
| Administrator | 123QWEqweqwe |
Babuk or LockBit 3.0? Rebranding Won’t Change the Code.
Analysis confirms that babuk.exe, advertised in the Babuk 2.0 Ransomware Affiliates Telegram channel, is actually based entirely on LockBit 3.0 source code—not Babuk. The sample shows key techniques identical to previous LockBit 3.0 variants, reinforcing that this is yet another case of threat actors rebranding existing ransomware rather than introducing anything genuinely new.
Key Overlapping Techniques
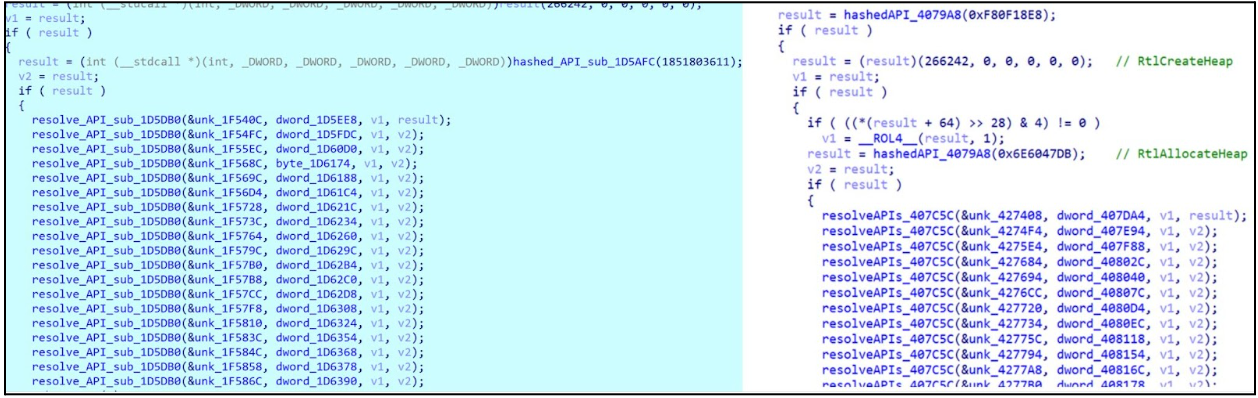
The analyzed sample uses API harvesting by hashing API names from DLLs and comparing them against a predefined list of required APIs (Figure 7). This technique, likely to obfuscate API calls and evade detection, mirrors the approach seen in Lockbit3.0/Black and aligns with previous findings by Trend Micro.
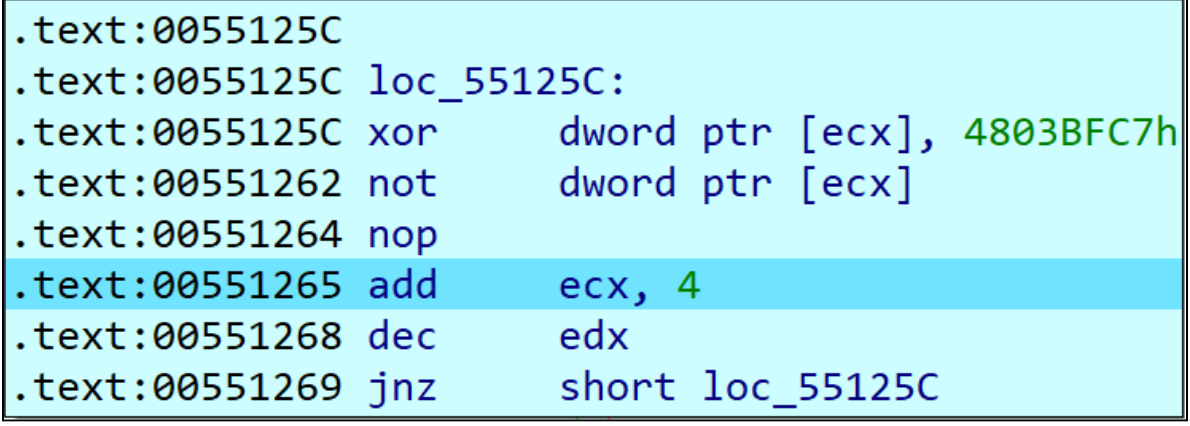
Likewise, The XOR key 0x4803BFC7 LockBit 3.0 used for renaming APIs is the same as it was reported before. The xor key is re-used multiple times in the code.
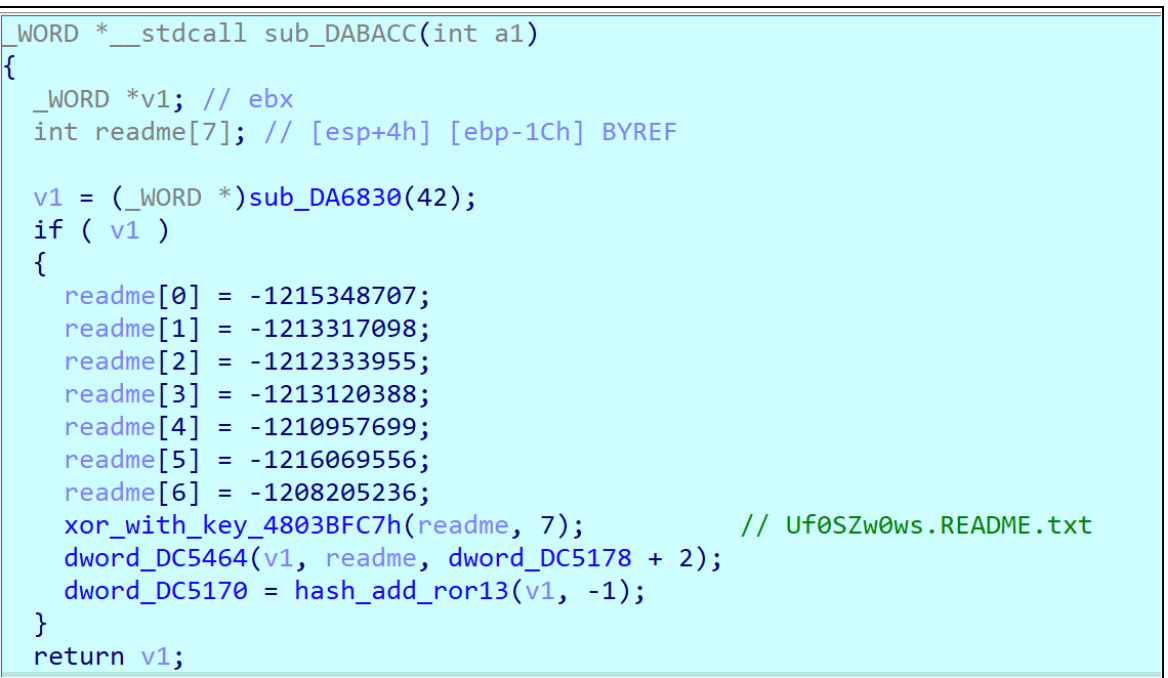
Additionally, the ransom note creating routine is identical as in previous Lockbit3.0/Black samples.
Like previous LockBit 3.0/ Black samples, the analyzed variant modifies the desktop wallpaper to display a ransom note—branded, unsurprisingly, as "LockBit Black" (not Babuk, in case anyone was still confused). It also appends specific extensions to encrypted files, changes their icons, and drops a .ico file in the %PROGRAMDATA% directory, staying true to the LockBit playbook.
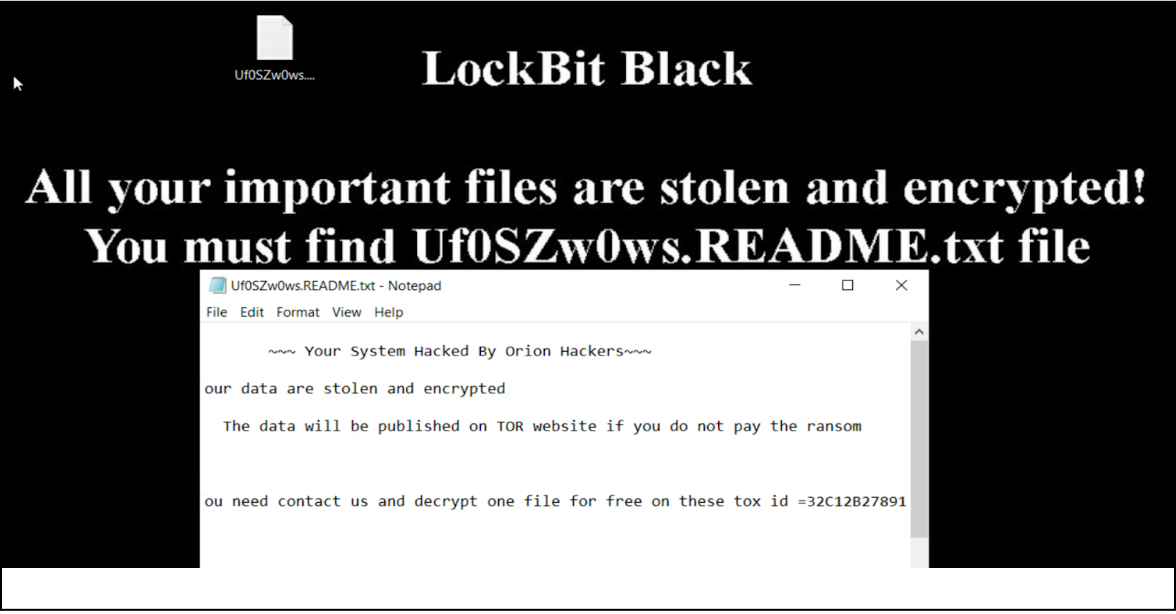
The ransom note referenced "Orion Hackers" and the tox ID 32C12B278912E26E5EAC57AEBB3F4FF16F0E31603C7B9D46AC02E9D993EE14351CEC3AB5945C. A search on this TOX ID linked the ransom demands to the `Babuk 2.0 Affiliate Group` on Telegram. Additionally, we discovered that messages from this channel were being reposted by an actor named Bjorkanism, who is actively sharing content from Affiliate Group Babuk 2.0 which is actually leaked Lockbit3.0.
Victimology
The new Babuk Locker 2.0 has recently been making waves within the cybersecurity and intelligence scene, claiming dozens of high-profile cyberattacks in a short time of less than two months of operation. Since January 2025, the group has listed at least 100 organizations as their alleged victims. Among their alleged victims are Amazon, the Israeli Knesset, Sodexo, and other high-profile organizations. Victims are from multiple sectors including energy, manufacturing, IT, government, etc.

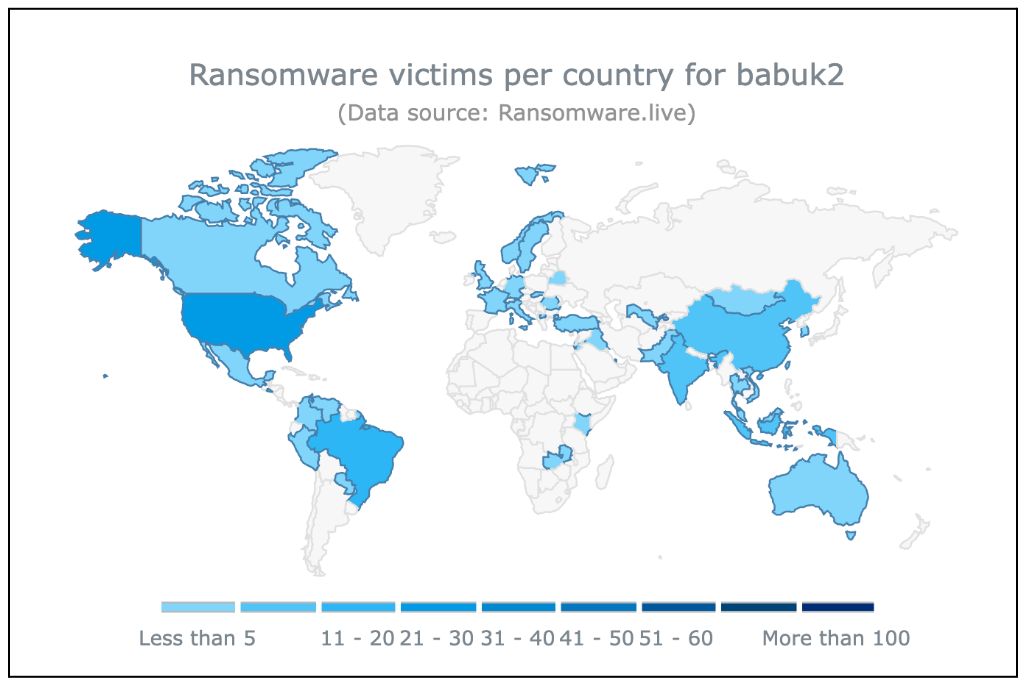
There have been growing claims of overlaps between Babuk Locker 2.0 and other ransomware groups, as some of their alleged victims were already attacked by other groups, such as HellCat, RansomHub, FunkSec, and others. These overlaps in victimology reinforce concerns about the authenticity of the new Babuk group entity and its operations.
Conclusion
Babuk Locker 2.0 is not a true revival of the original Babuk group—it’s just LockBit 3.0 with a new label. Our analysis strongly suggests that Skywave and Bjorka are behind this operation, either as collaborators or opportunistic actors riding the same wave.
Despite its bold claims, Babuk 2.0’s victim list overlaps heavily with other ransomware groups, raising doubts about the legitimacy of its attacks. Rather than a sophisticated new threat, this looks more like a rebranding stunt—a common tactic among ransomware operators to confuse defenders, attract affiliates, and inflate their reputation.
This case reinforces a familiar pattern: ransomware groups don’t disappear—they just change names, recycle code, and keep cashing in. Whether Skywave and Bjorka are working together or simply using Babuk’s name for credibility, one thing is clear: Babuk 2.0 is just LockBit 3.0 in a different costume.
IOCs (Indicators of Compromise)
| DLS (Data Leak Sites) |
|---|
| 7dikawx73goypgfi4zyo5fcajxwb7agemmiwqax3p54aey4dwobcvcyd.onion |
| imblth46g3x5oo444wkjn7umj4g26tnhmrlo53ovfqmmkmughdw4j2ad.onion |
| bxwu33iefqfc3rxigynn3ghvq4gdw3gxgxna5m4aa3o4vscdeeqhiqad.onion |
| Telegram Handles |
| @OfficialBabukLocker |
| @BabukLockerRaasSHA1 |
| @BabukLockerRaas (inactive) |
| @BGLocker |
| Tox ID & Contact |
| Tox: 022A7EEB83B648F55DA7A6BEFD130C2156C74F3501A31D853234EC2D18E77A1E5BEC7F60201 |
| Email: [email protected] |
| YouTube: youtube.com/@babuklocker |
| Ransomware samples obtained from Telegram channels |
| 3facc153ed82a72695ee2718084db91f85e2560407899e1c7f6938fd4ea011e9 |
| bdc482583a330a4682d13bfb7a0cf75b2fa350ac536064bce7b2bdd9d875de4a |
| 0192eaf2ea5a52fa9d2398b3a2f69c163d47b368cd131ccae60df0a98c1fa2ca |
Source: Rapid7
Source Link: https://blog.rapid7.com/2025/04/02/a-rebirth-of-a-cursed-existence-the-babuk-locker-2-0/