
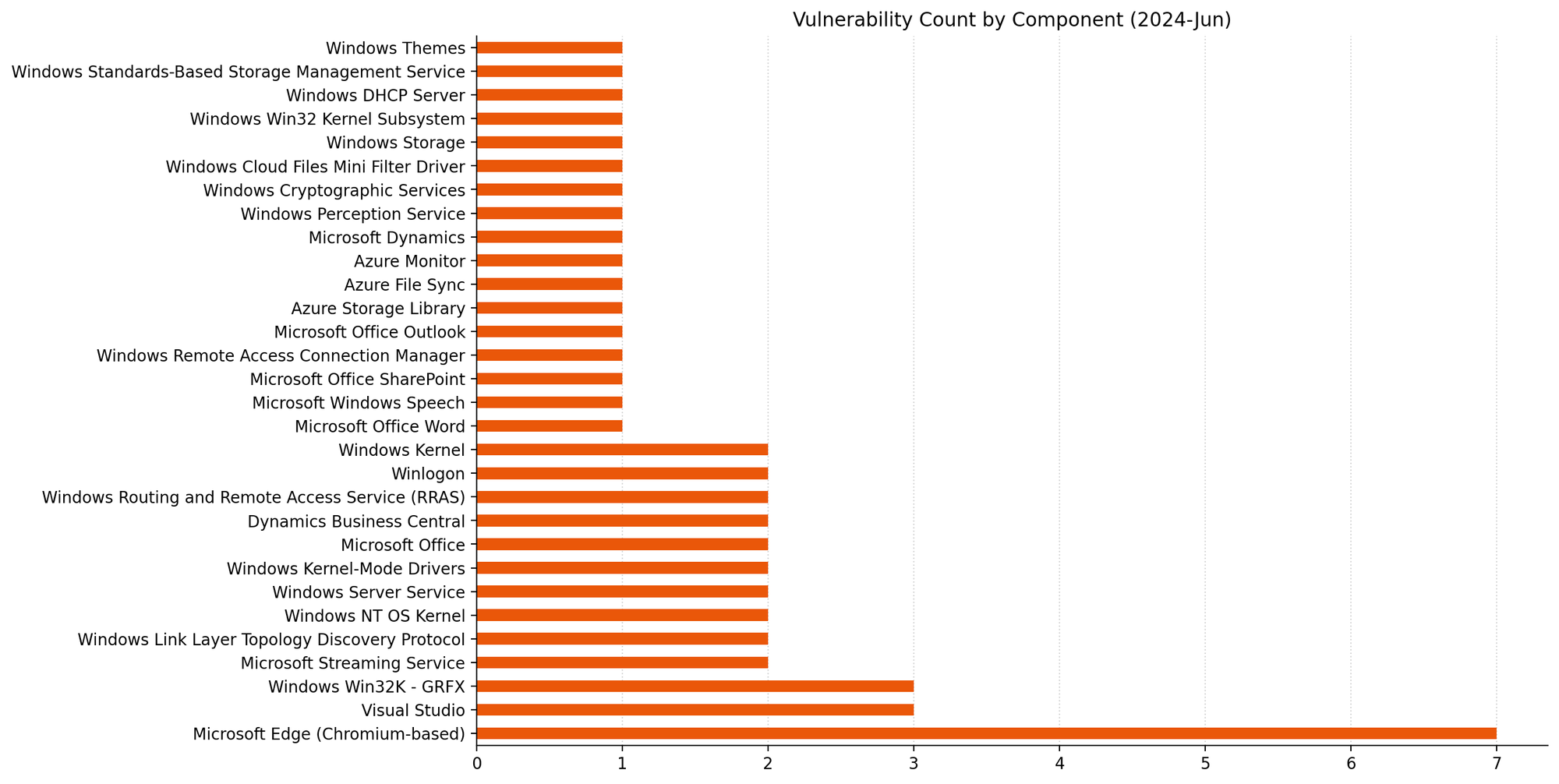
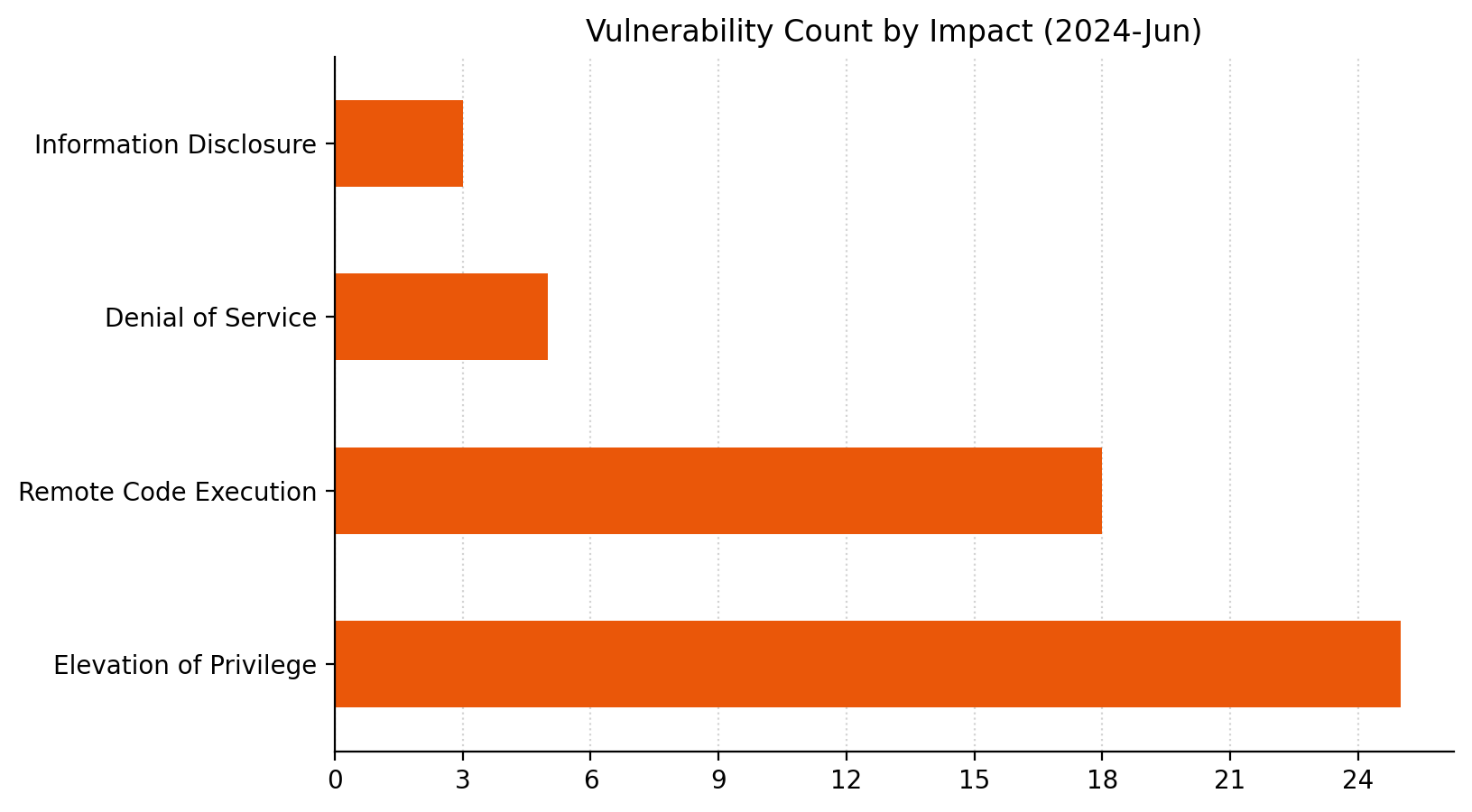
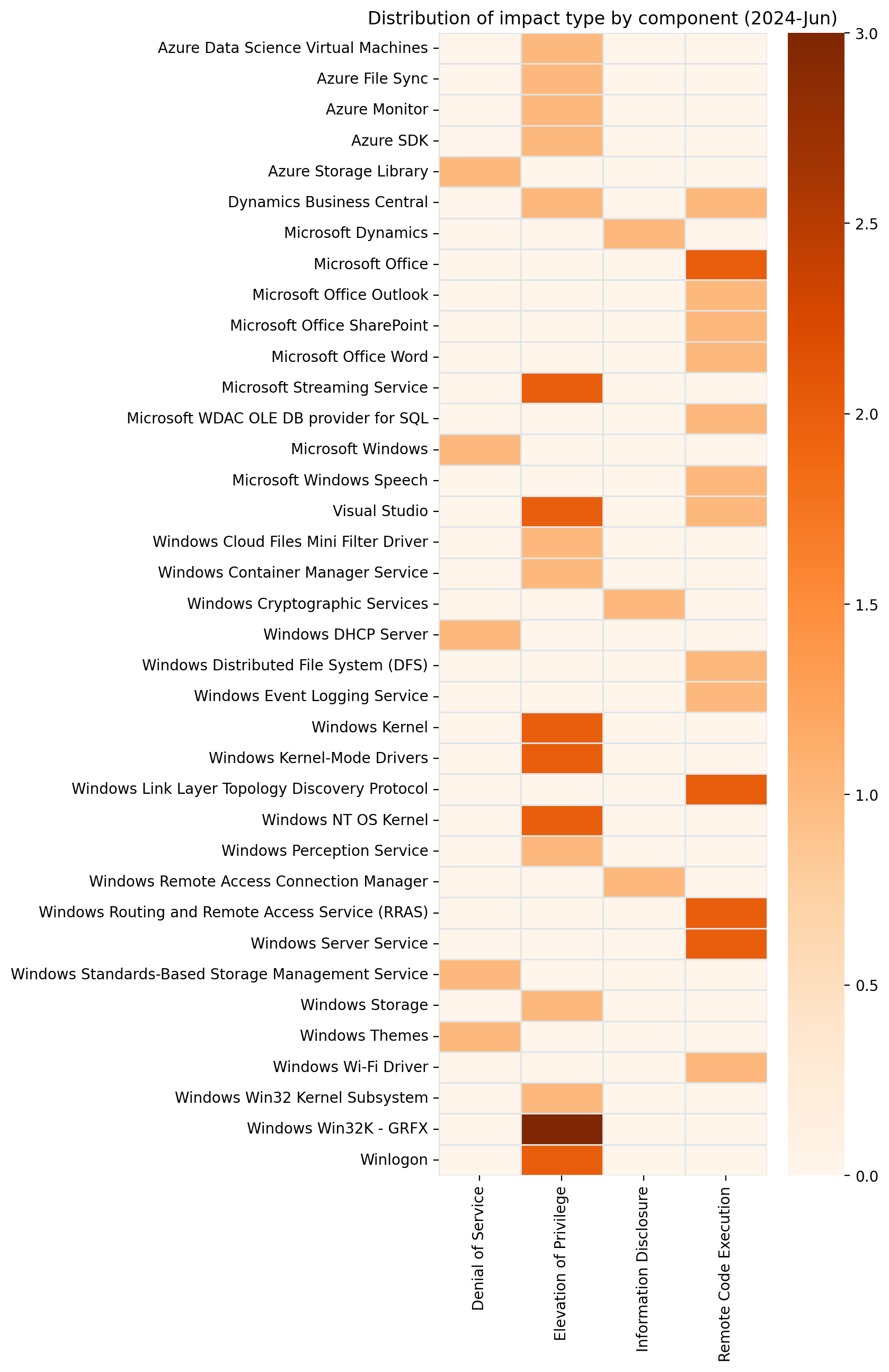
It’s June 2024 Patch Tuesday. Microsoft is addressing 51 vulnerabilities today, and has evidence of public disclosure for just a single one of those. At time of writing, none of the vulnerabilities published today are listed on CISA KEV, although this is always subject to change. Microsoft is patching a single critical remote code execution (RCE) vulnerability today. Seven browser vulnerabilities were published separately this month, and are not included in the total.
MSMQ: critical RCE
The sole critical RCE patched today is CVE-2024-30080 for all current versions of Windows. Exploitation requires that an attacker send a specially crafted malicious packet to an MSMQ server, which Patch Tuesday watchers will know as a perennial source of vulnerabilities. As usual, Microsoft points out that the Windows message queuing service is not enabled by default; as usual, Rapid7 notes that a number of applications – including Microsoft Exchange – quietly introduce MSMQ as part of their own installation routine. As is typical of MSMQ RCE vulnerabilities, CVE-2024-30080 receives a high CVSSv3 base score due to the network attack vector, low attack complexity, and lack of required privileges. Code execution is presumably in a SYSTEM context, although the advisory does not specify.
Office: malicious file RCEs
Microsoft Office receives patches for a pair of RCE-via-malicious-file vulnerabilities. CVE-2024-30101 is a vulnerability in Outlook; although the Preview Pane is a vector, the user must subsequently perform unspecified specific actions to trigger the vulnerability and the attacker must win a race condition. On the other hand, CVE-2024-30104 does not have the Preview Pane as a vector, but nevertheless ends up with a slightly higher CVSS base score of 7.8, since exploitation relies solely on the user opening a malicious file.
SharePoint: RCE
This month also brings a patch for SharePoint RCE CVE-2024-30100. The advisory is sparing on details, and the context of code exploitation is not clear. The weakness is described as CWE-426: Untrusted Search Path; many (but not all) vulnerabilities associated with CWE-426 lead to elevation of privilege.
DNSSEC NSEC3: CPU exhaustion DoS
And now for something completely different: CVE-2023-50868, which describes a denial of service vulnerability in DNSSEC. This vulnerability is present in the DNSSEC spec itself, and the CVE was assigned by MITRE on behalf of DNSSEC. Microsoft’s implementation of DNSSEC is thus subject to the same attack as other implementations. An attacker can exhaust CPU resources on a DNSSEC-validating DNS resolver by demanding responses from a DNSSEC-signed zone, if the resolver uses NSEC3 to respond to the request. NSEC3 is designed to provide a safe way for a DNSSEC-validating DNS resolver to indicate that a requested resource does not exist. Under certain circumstances, the DNS resolver must perform thousands of iterations of a hash function to calculate an NSEC3 response, and this is the foundation on which this DoS exploit rests. All current versions of Windows Server receive a patch today.
Typically, when Microsoft publishes a security advisory and describes the vulnerability as publicly disclosed, that public disclosure will have been recent. However, in the case of CVE-2023-50868, the flaw in DNSSEC was first publicly disclosed on 2024-02-13. The advisory acknowledges four academics from the German National Research Centre for Applied Cybersecurity (ATHENE), which is perhaps of interest since these same researchers are authors on a March 2024 academic paper that downplays the DoS potential of CVE-2024-50868. Those same researchers published another DNSSEC flaw CVE-2023-50387 (also known as KeyTrap) in January 2024, which they describe as having potentially serious implications; Microsoft patched that one at the next scheduled opportunity in February. The CVE-2023-50868 advisory published today does not provide further insight as to why this vulnerability wasn’t patched sooner; a reasonable assumption might be that Microsoft assesses CVE-2023-50868 as less urgent/critical than CVE-2023-50387, although both receive a rating of Important on Microsoft’s proprietary severity ranking scale. It’s also possible that Microsoft does not wish to be the only major server OS vendor without a patch.
Lifecycle update
There are no significant changes to the lifecycle phase of Microsoft products this month. In July, Microsoft SQL Server 2014 will move past the end of extended support. From August onwards, Microsoft only guarantees to provide SQL Server 2014 security updates to customers who choose to participate in the paid Extended Security Updates program.
Summary Charts
Summary Tables
Azure vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-37325 | Azure Science Virtual Machine (DSVM) Elevation of Privilege Vulnerability | No | No | 8.1 |
| CVE-2024-35252 | Azure Storage Movement Client Library Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-35254 | Azure Monitor Agent Elevation of Privilege Vulnerability | No | No | 7.1 |
| CVE-2024-35255 | Azure Identity Libraries and Microsoft Authentication Library Elevation of Privilege Vulnerability | No | No | 5.5 |
| CVE-2024-35253 | Microsoft Azure File Sync Elevation of Privilege Vulnerability | No | No | 4.4 |
Browser vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-5499 | Chromium: CVE-2024-5499 Out of bounds write in Streams API | No | No | N/A |
| CVE-2024-5498 | Chromium: CVE-2024-5498 Use after free in Presentation API | No | No | N/A |
| CVE-2024-5497 | Chromium: CVE-2024-5497 Out of bounds memory access in Keyboard Inputs | No | No | N/A |
| CVE-2024-5496 | Chromium: CVE-2024-5496 Use after free in Media Session | No | No | N/A |
| CVE-2024-5495 | Chromium: CVE-2024-5495 Use after free in Dawn | No | No | N/A |
| CVE-2024-5494 | Chromium: CVE-2024-5494 Use after free in Dawn | No | No | N/A |
| CVE-2024-5493 | Chromium: CVE-2024-5493 Heap buffer overflow in WebRTC | No | No | N/A |
Developer Tools vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-29187 | GitHub: CVE-2024-29187 WiX Burn-based bundles are vulnerable to binary hijack when run as SYSTEM | No | No | 7.3 |
| CVE-2024-29060 | Visual Studio Elevation of Privilege Vulnerability | No | No | 6.7 |
| CVE-2024-30052 | Visual Studio Remote Code Execution Vulnerability | No | No | 4.7 |
ESU vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-30074 | Windows Link Layer Topology Discovery Protocol Remote Code Execution Vulnerability | No | No | 8 |
| CVE-2024-30075 | Windows Link Layer Topology Discovery Protocol Remote Code Execution Vulnerability | No | No | 8 |
Microsoft Dynamics vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-35249 | Microsoft Dynamics 365 Business Central Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-35248 | Microsoft Dynamics 365 Business Central Elevation of Privilege Vulnerability | No | No | 7.3 |
| CVE-2024-35263 | Microsoft Dynamics 365 (On-Premises) Information Disclosure Vulnerability | No | No | 5.7 |
Microsoft Office vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-30103 | Microsoft Outlook Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-30100 | Microsoft SharePoint Server Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-30104 | Microsoft Office Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-30101 | Microsoft Office Remote Code Execution Vulnerability | No | No | 7.5 |
| CVE-2024-30102 | Microsoft Office Remote Code Execution Vulnerability | No | No | 7.3 |
Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-30064 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 8.8 |
| CVE-2024-30068 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 8.8 |
| CVE-2024-30097 | Microsoft Speech Application Programming Interface (SAPI) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-30085 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-30089 | Microsoft Streaming Service Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-30072 | Microsoft Event Trace Log File Parsing Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-35265 | Windows Perception Service Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-30088 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-30099 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-30076 | Windows Container Manager Service Elevation of Privilege Vulnerability | No | No | 6.8 |
| CVE-2024-30096 | Windows Cryptographic Services Information Disclosure Vulnerability | No | No | 5.5 |
| CVE-2024-30069 | Windows Remote Access Connection Manager Information Disclosure Vulnerability | No | No | 4.7 |
Windows ESU vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-30080 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability | No | No | 9.8 |
| CVE-2024-30078 | Windows Wi-Fi Driver Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-30077 | Windows OLE Remote Code Execution Vulnerability | No | No | 8 |
| CVE-2024-30086 | Windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-30062 | Windows Standards-Based Storage Management Service Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-30094 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-30095 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-35250 | Windows Kernel-Mode Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-30082 | Win32k Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-30087 | Win32k Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-30091 | Win32k Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-30083 | Windows Standards-Based Storage Management Service Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2023-50868 | MITRE: CVE-2023-50868 NSEC3 closest encloser proof can exhaust CPU | No | Yes | 7.5 |
| CVE-2024-30070 | DHCP Server Service Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-30093 | Windows Storage Elevation of Privilege Vulnerability | No | No | 7.3 |
| CVE-2024-30084 | Windows Kernel-Mode Driver Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-30090 | Microsoft Streaming Service Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-30063 | Windows Distributed File System (DFS) Remote Code Execution Vulnerability | No | No | 6.7 |
| CVE-2024-30066 | Winlogon Elevation of Privilege Vulnerability | No | No | 5.5 |
| CVE-2024-30067 | Winlogon Elevation of Privilege Vulnerability | No | No | 5.5 |
| CVE-2024-30065 | Windows Themes Denial of Service Vulnerability | No | No | 5.5 |
Source: Rapid7
Source Link: https://blog.rapid7.com/2024/06/11/patch-tuesday-june-2024/